We are excited to introduce a brand new experience in Office 365—Office 365 Planner, which offers people a simple and highly visual way to organize teamwork. Planner makes it easy for your team to create new plans, organize and assign tasks, share files, chat about...
BLOG
Home »
Maximizing Laptop Battery Life
There is nothing quite as annoying as getting a message from your laptop that your battery is about to run out. Even with the longer lasting laptop batteries of today, there will be an occasion where you need every last second from it, and maybe even a little more....
10 Most Important Work Skills In 2020
BYOD is Dead – Long Live CYOD!
There are only a few people who would argue the benefits of BYOD. When employees are allowed to bring their computers and smart devices to work, it saves their employers from having to buy and maintain the devices and infrastructure needed to support them, creating...
Inserting and Using Drop Down Lists in Excel
A helpful tool when working in Excel spreadsheets is the drop down codes. These can be used a variety of ways. For this example we’ll use a spreadsheet with names and address that we are tracking for how a customer was contacted. In the Status column I want drop down...
5 Fast Fixes for Pressing Problems
Time has a way of sneaking up on us. Despite the flow of time being one of the most dependable things in life, it can still come as a shock to find out that the fax machine was invented the same year people were traveling the Oregon Trail, or that there is more...
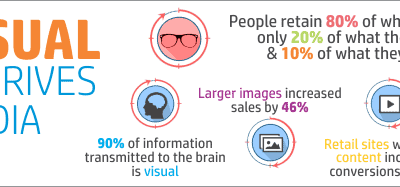
How Visual Content Drives Social Media Growth
Office Mobile Gets In "Touch" With Windows 10
Microsoft has released Office Mobile apps as part of the worldwide rollout of Windows 10. Tablet users with Windows 10 can enjoy free access to the mobile versions of Microsoft’s popular Word, Excel, PowerPoint and OneNote applications. The mobile version of these...